Early warning signs and pre-emptive
remediation of critical security issues
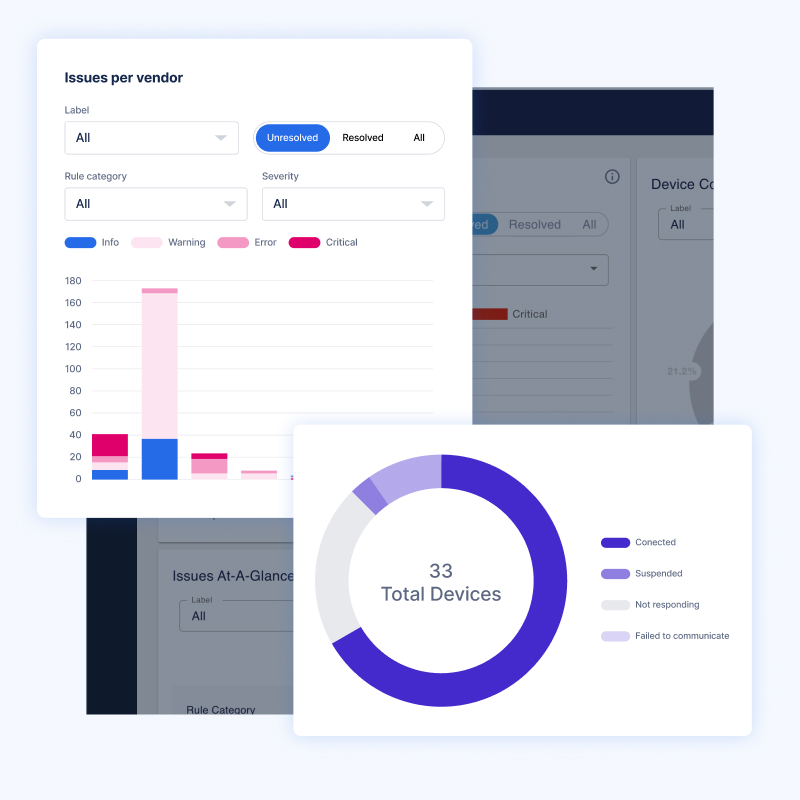
Proactively identify and resolve issues across your firewalls and security infrastructure—to accelerate troubleshooting, prevent downtime, and reduce the strain on IT operations teams.
Benefits
Solve issues before they impact service delivery
Proactively identify misconfigurations, high availability inconsistencies, forgotten maintenance tasks, and other best practices to avoid changes.
Optimize security infrastructure performance
Streamline IT operations with automation so teams can focus on optimizing security services elsewhere.
Reduce mean time
to resolution
Streamline IT operations with automation so teams can focus on optimizing security services elsewhere.
Stay on top of
best practices
Automatically assess devices for alignment with changing configuration recommendations from vendors and the knowledge of a community of network practitioners.
Automate
maintenance
Reduce errors and save time when you automate routine tasks like configuration backups and checking for license expiration.
Automate verification
of change requests
Ensure that upgrades and changes are implemented without issues, minimizing costly disruptions.
Key Features
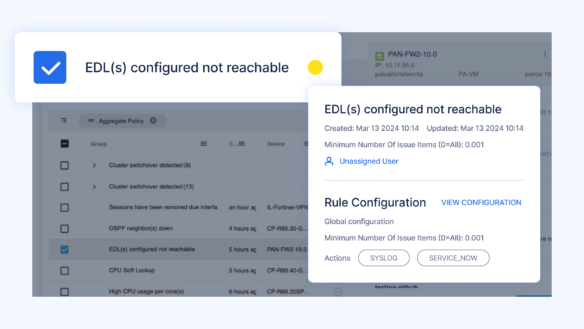
Stateful health checking
Continuously assess the health of your address manager and DNS/DHCP servers to preemptively find and address issues like:
- DNS lookup failure
- DHCP scope exhaustion
- Zone transfer failure
Critical service connectivity
Ensure communication with critical external services (like Syslog services; NTP, DNS, and identity servers; and threat prevention policies) is available at all times.
Misconfigurations
Verify configurations against gold standard frameworks to identify and resolve configuration drift issues like:
- DNS server configuration doesn’t match address manager
- NTP/DNS/Syslog server configured doesn’t match requirement
- Manual override enabled
High availability readiness
Find cross-device inconsistencies that jeopardize high availability, such as:
- Alerts if xHA server, cluster, or cluster member is down
- Identify if xHA configuration is not synchronized
- Identify if DHCP failover state has changed, or if failover servers are down
Auto-detect security risks and ensure compliance
Use hundreds of automation elements and security control validations to find security risks and compliance violations.
Automate maintenance tasks
Maintenance tasks seldom feel like the most urgent item on the ever-growing to-do list, but they’re critical to maintaining service availability. Automate tasks like identifying certificate renewal needs to avoid service disruptions and device configuration backup to maintain firewall health and performance.
Automated troubleshooting
Automatically apply proven, device-specific domain knowledge to analyze the root causes of issues as they occur.
Ready to start?
Drive automatic security, reliability, and availability
across your network and security infrastructure.
Network Security Vendors
Cisco ASA Firewalls Solution
Radware Solution
Juniper Solution
Palo Alto Networks Solution
Check Point Firewall Solution
F5 Networks Solution
Symantec Blue Coat
Fortinet Solution
LiveNX Assurance – Network Security
Reactive monitoring vs. proactive prevention
SNMP-based monitoring and observability tools are fundamentally reactive. They only understand lagging indicators of risk or underperformance (i.e. events that have already happened).
Infrastructure Assurance is proactive, not reactive. It continuously listens for leading indicators of risk or underperformance (i.e. events that haven’t happened yet) and recommends preventive actions. You can even configure CLI commands and API queries to auto-triage issues.
Resources
Solution Brief
LiveNX Assurance for
Palo Alto Next-Gen Firewalls
Datasheet
LiveNX Assurance Datasheet
Blog
From Reactive to Proactive: 8 Critical Features for Firewall Monitoring Tools
LiveNX Assurance
See our firewall capabilities for yourself
Enough marketing already. Book a live demo of Infrastructure Assurance and get your technical questions answered.

